Counting Images, a FireFox Add-on
Many of my clients ask me to test their content management and processing systems. Often this involves investigating how the software handles images of various sizes as well as text of various lengths or types.
To help create test-images, I created this little FireFox Add-on. The Counting Images add-on starts with one click and can be used to create an image of a custom size.
For example: if you need a 300x250 MPU advert image - just enter 300 and 250 into the panel and click Create Image. To download the image, just click on it - as you would a a link and choose Save.
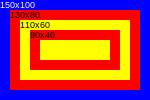
The image files are named widthxheight.png, and include markings to help identify if they have been truncated e.g.:
The marked numbers refer to the size in pixels of the rectangle they are in. E.g.: the blue rectangle (always the outermost one) is 150x100 pixels in size.
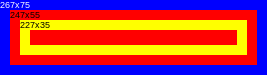
Another example:
As you can see the rectangles start at the defined size and count down in steps of 20 pixels.
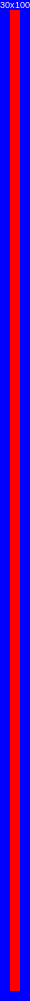
What could go wrong? Well a good example is very thing and tall images. The image edge might actually truncate the text specifiying its height e.g.:
The image here is 30x1001 but the narrowness means the visible text is 30x100.